A Lightweight and Efficient Authentication Scheme for the Internet of Drone Based on Cancelable Biometrics
Kangyi Chen
1,2
Weixin Bian
1,2,*
 Qingde Li
3
Dong Xie
1,2
Jinbin Meng
1,2
Qingde Li
3
Dong Xie
1,2
Jinbin Meng
1,2
Received: 10 January 2026 Revised: 30 January 2026 Accepted: 12 March 2026 Published: 01 April 2026
© 2026 The authors. This is an open access article under the Creative Commons Attribution 4.0 International License (https://creativecommons.org/licenses/by/4.0/).
1. Introduction
The Internet of Drones (IoD) is a layered architecture that enables coordinated access and communication for Unmanned Aerial Vehicles (UAVs), commonly referred to as drones, within a regulated airspace. A typical IoD system comprises drones, ground stations (GSs), and remote users, forming an interconnected ecosystem for aerial operations [1]. Initially deployed in military contexts, drones have since expanded into a broad range of civilian and industrial applications due to the miniaturization of sensors, advances in wireless communication, and growth in autonomous control technologies.
IoD applications now span urban traffic control, environmental monitoring, search and rescue operations, agriculture, industrial inspection, logistics, public safety, and even emergency healthcare delivery [2]. By equipping drones with high-precision sensors and integrating big data analytics and artificial intelligence (AI) capabilities, UAVs can perform complex tasks such as autonomous navigation, real-time anomaly detection, and cooperative swarm coordination with minimal human intervention. This improves operational precision, reduces human error, and enhances responsiveness in time-sensitive scenarios.
From a network perspective, the Air Traffic Networks (ATNs) offer significantly greater spatial freedom than traditional Ground Transportation Networks (GTNs). The rational exploitation of ATNs can relieve congestion in GTNs and open new paradigms for real-time, on-demand services in smart cities. According to Drone Industry Insights, the global drone market is projected to reach $54.6 billion by 2030, with a compound annual growth rate (CAGR) of 7.7%, indicating a robust upward trajectory.
However, the rapid proliferation of IoD technologies introduces critical challenges in security and privacy protection [3]. Due to their reliance on open wireless communication, drones are vulnerable to eavesdropping, jamming, replay attacks, spoofing, and signal injection. GPS spoofing can mislead navigation, and vulnerabilities in Wi-Fi protocol stacks create opportunities for unauthorized access. Moreover, drones often communicate with ground stations and remote servers over insecure channels such as Wi-Fi or Long Term Evolution (LTE), where conventional security assumptions may no longer hold.
To mitigate these threats, robust authentication, key agreement, and data integrity mechanisms must be integrated into the IoD framework. In response to these challenges, this paper proposes a multi-factor authentication and key agreement scheme, which incorporates Cancelable Biometric techniques and a Physically Unclonable Function (PUF) update mechanism. The approach aims to strengthen identity verification, support revocability of compromised biometric templates, and enhance resilience against physical and cyber-attacks. The scheme is designed to provide mutual authentication, session key establishment, and protection against impersonation, replay, and template inversion attacks, thereby achieving a balance between lightweight performance and high security assurance in IoD environments.
1.1. Related Work
A key component of securing IoD systems is robust authentication. However, many authentication and key agreement (AKA) protocols neglect biometric protection. Remote biometric authentication systems often face four main threats: sensor spoofing, database attacks, comparator attacks, and channel interception [4]. Cancelable biometrics enhance system security by transforming original biometric templates into protected representations in a secure domain, preventing the leakage of original samples [5]. Comparisons are performed within this domain to ensure data protection during identification.
Traditional authentication relies on passwords, which burden users and are prone to guessing attacks [6]. Therefore, we adopt biometrics, which serve as unique, hard-to-replicate identifiers [7]. Teoh [8] proposed Multispace Random Projections (MRP), a widely used method for cancelable template generation [9]. However, stolen projection matrices can allow reconstruction of the original biometrics. Index-of-Max Hashing (IoM) [10] is a classical method that maps biometric features into index-domain hash codes using gaussian random projection (GRP) or uniformly random permutation (URP) to generate secure templates. Kuzu et al. [11] applied deep learning to create cancelable finger vein templates, showing high robustness. Cancelable biometrics exhibit cancelability (template regeneration via parameter change), non-invertibility (blocking reconstruction), diversity (preventing cross-system linkability), and accuracy (maintaining recognition performance) [7].
Authentication schemes have evolved to multi-factor approaches that combine biometrics, smart cards, and auxiliary data for enhanced security [12]. A secure AKA protocol is crucial for pre-communication key agreement over insecure channels, especially in UAV networks. In 2021, Srinivas et al. [13] proposed UAP-BCIoT, a three-factor authentication protocol enabling mutual authentication and key agreement for smart transportation. Sarier [14] proposed MFBA, integrating zero-knowledge proofs and homomorphic encryption to perform biometric comparison in encrypted space. However, storing transformation parameters on the smart card risks biometric leakage.
Recently, drone communications over wireless channels have gained attention. However, these channels expose drones to security threats [15]. Unlike traditional authentication protocols, our design supports dynamic key generation during mutual authentication. Gope et al. [16] introduced a PUF-based authentication with an update mechanism, enhancing resistance against attacks. Their scheme leverages physical-layer security for sensor networks. Due to limited drone resources, many lightweight protocols [17] sacrifice robustness. Liu et al. [18] proposed a PUF-based lightweight protocol without challenge-response pairs (CRP) update, while others adopt ECC and hash functions for efficient key management [19]. Despite PUF’s popularity in IoT and IoD, few protocols integrate it with biometric protection. Given PUF’s support for irreversibility, unlinkability, and reproducibility (key cancelable biometric requirements), this combination is promising. Bian et al. [20] confirmed its feasibility by integrating PUF and fuzzy extractors for secure template generation.
Table 1 presents the Gap Analysis and provides brief descriptions of 11 identity authentication-related research papers. The columns include Scheme/Year, Template Protection, Cancelable Property, PUF Usage, CRP Updateability, Formal Proof (ROR Model), Formal Verification (AVISPA Tool), Attack Coverage, and Dataset-Based Evaluation. This structure renders the novelty, security, and efficiency claims of the proposed scheme traceable and persuasive.
Table 1. Gap Analysis.
|
Scheme/Year |
Template Protection |
Cancelable Property |
PUF Usage |
CRP Updateability |
ROR |
AVISPA |
Attack Coverage |
Dataset-Based Evaluation |
|---|---|---|---|---|---|---|---|---|
|
Das [12]/2009 |
Unused |
No |
Unused |
No |
Unused |
Unused |
A4–12 |
Unused |
|
Srinivas [13]/2021 |
Primitive Biometric |
No |
Unused |
No |
Yes |
Unused |
A1–12 |
Unused |
|
Sarier [14]/2010 |
Cancelable Biometric |
No |
Unused |
No |
Unused |
Unused |
A4–8, A10, A11, A13 |
Unused |
|
Kirsal Ever [15]/2019 |
Unused |
No |
Unused |
No |
Unused |
Unused |
A1, A2, A4–12 |
Unused |
|
Gope [16]/2019 |
Primitive Biometric |
No |
Yes |
No |
Yes |
Unused |
A1–12 |
Unused |
|
Chaudhary [17]/2023 |
Unused |
No |
Unused |
No |
Yes |
Unused |
A1–12 |
Unused |
|
Liu [18]/2020 |
Primitive Biometric |
No |
Yes |
No |
Yes |
Unused |
A1, A3–12 |
Unused |
|
Tanveer [19]/2022 |
Primitive Biometric |
No |
Unused |
No |
Yes |
Yes |
A1–12 |
Unused |
|
Bian [20]/2020 |
Primitive Biometric |
No |
Yes |
No |
Unused |
Unused |
A1, A2, A4–8, A10, A11 |
Unused |
|
Zhang [21]/2021 |
Cancelable Biometric |
Yes |
Yes |
No |
Yes |
Unused |
A1–13 |
FVC |
|
Hu [22]/2024 |
Cancelable Biometric |
Yes |
Yes |
Yes |
Yes |
Unused |
A1–13 |
FVC |
A1: User Anonymity; A2: Forward Secrecy; A3: Sensor Anonymity; A4: Replay Attack; A5: Man-in-the-Middle Attack; A6: Physical Attack; A7: Device Loss Attack; A8: Known session Key attack; A9: Password Guessing Attack; A10: User Device Loss Attack; A11: Offline Attack; A12: Sensor Theft Attack; A13: Biometric Attack; FVC: Fingerprint Verification Competition Datasets.
1.2. Motivation and Contribution
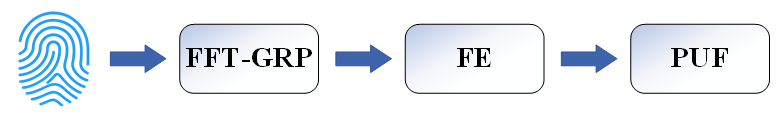
Addressing the various limitations of identity authentication in IoD, we have designed a new protocol to meet the challenges. In this protocol, we employ a cancelable biometric template protection method to safeguard biometric data. Specifically, the contributions of our paper are as follows:
- (1)
-
Combined with Fast Fourier Transform (FFT), IoM hash, Fuzzy extractor (FE), and Physical Unclonable Function (PUF), this paper proposes a better method for generating cancelable biometric templates.
- (2)
-
This paper proposes a lightweight mutual authentication protocol using cancelable biometrics with PUF updates and a single challenge-response pair (CRP), optimized for resource-limited IoD.
- (3)
-
Provide a formal security analysis based on the ROR model. Additionally, the security analysis indicates that the protocol can resist many attacks.
The rest of this article is organized as follows: Section 3 provides preliminary information. Section 4 describes the proposed template protection process and the proposed authentication scheme. Section 5 analyzes the security performance of the proposed scheme. Section 6 describes the experiments performed and the associated performance analysis. This article is summarized in Section 7.
2. System Model
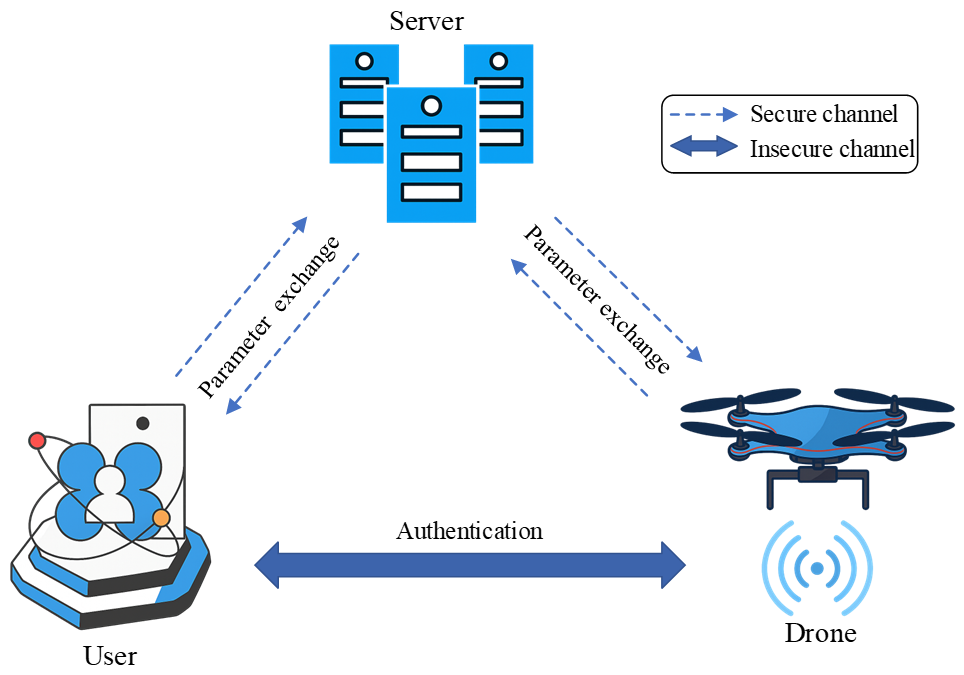
2.1. Network Model
This section describes the network model and the adversary model in detail.
As shown in Figure 1, the network architecture is composed of three parts: (i) users (Ui), equipped with mobile devices integrated with biometric scanners (e.g., fingerprint sensors) and smart cards (SC) for local storage of authentication parameters $$\left(A,{ID}_{cs}^{\mathrm{\prime}},RPW,{\mathrm{\tau }}_{i}\right)$$. (ii) Control center server (CS), a fully trusted entity responsible for generating global keys $${K}_{global}$$, challenges $$\left({C}_{u},{C}_{d}\right)$$, pseudo-identities $$\left({PID}_{u},{PID}_{d}\right)$$, and storing registration data $$\left({PID}_{u},\left({C}_{u},{R}_{u}\right)\right)$$, $$\left({ID}_{d},{PID}_{d},\left({C}_{d},{R}_{d}\right)\right)$$. and (iii) Drones ($${RD}_{j}$$), resource-constrained devices that register with CS to obtain authentication credentials, store $${PID}_{d}$$ locally, and execute PUF-based challenge-response mechanisms. The operator must carry a mobile device to receive data and store it locally for use during registration or mutual authentication processes. The CS is a trusted entity that generates auxiliary parameters for both $${U}_{i}$$ and $${RD}_{j}$$; it is also needed to store the registered IDs or pseudo-IDs of $${U}_{i}$$ and $${RD}_{j}$$.
The drone also needs to register with the CS to obtain key data for mutual authentication. If $${U}_{i}$$ and $${RD}_{j}$$ successfully complete the session key agreement through the CS, and a temporary session key will be generated for secure data communication.
2.2. Adversary Model
The core assumptions of the system are as follows: Communication between users (Ui), the control server (CS), and drones (Dj) is conducted via insecure public channels such as Wi-Fi and LTE, which are vulnerable to interception and tampering; user smart cards and drones are untrusted and may be lost or stolen, and the data stored locally on them can be extracted through side-channel attacks (e.g., power analysis); the control server is immune to all attacks and maintains the data integrity of the stored registration information.
This article adopts the widely used Dolev–Yao (DY) threat model for analyzing the security of cryptographic protocols [23]. Our protocol involves three types of participants: users (Ui), the control server (CS), and drones ($${RD}_{j}$$), each with multiple instances. The DY model assumes that an adversary $$\mathcal{A}$$ having multiple instances:
- (1)
-
Public Channel Control: Intercept, modify, delete, inject, or replay messages transmitted over public channels (supporting replay attacks and man-in-the-middle attacks), while being unable to access information exchanged via secure channels.
- (2)
-
Compromised Entity Exploitation: The CS is fully trusted and immune to attacks, but other entities (users and drones) may be compromised; user smart cards (SC) may be lost or stolen, with sensitive data $$\left(A,{ID}_{cs}^{\mathrm{\prime}},RPW,{\mathrm{\tau }}_{i}\right)$$ extractable via side-channel attacks (e.g., power analysis), and the drone’s memory can be compromised to obtain stored $${PID}_{d}$$ and historical Challenge-Response Pairs $$\left({C}_{d},{R}_{d}\right)$$.
- (3)
-
Parameter Leakage: Partially acquire transformation parameters (e.g., partial Gaussian random projection matrices, random permutation arrays r) but not the complete set.
- (4)
-
Tampering Attacks: Manipulate timestamps ($${\mathrm{t}}_{1}$$–$${\mathrm{t}}_{6}$$) in authentication messages to bypass freshness checks; forge PUF responses if CRPs are leaked.
- (5)
-
Guessing Attacks: Launch online or offline password guessing attacks using a finite password dictionary (DC) and a biometric feature space.
3. Preliminaries
3.1. Fuzzy Extractor
Fuzzy extractor (FE) is a cryptographic tool used to extract and reproduce a reliable and random key from noisy data. There are two functions, FE.Gen(·) and FE.Rep(·) [20]. Enter the biometric Bi to FE.Gen(·) to generate auxiliary data $$\sigma$$ and key $$\tau$$, denoted as ($$\sigma$$, $$\tau$$) = FE.Gen(Bi). If the subsequently extracted biometric is sufficiently similar to Bi, the $$\sigma$$ can be recovered by FE.Rep($${Bi}^{\mathrm{\prime}}$$, $$\tau$$). FE is not sensitive to noise, as long as $$\mathrm{d}\mathrm{i}\mathrm{s}\left(Bi,{Bi}^{\mathrm{\prime}}\right)<t$$, the same ($$\sigma$$, $$\tau$$) can be generated [21]. FE can effectively address the issue of minor differences in biometric features during the registration and authentication phases.
3.2. Cancelable Biometric
Cancelable biometrics enhance the security and privacy of biometric systems by transforming the original biometric vector $$\mathbf{x}\in {\mathbb{R}}^{n}$$ into a protected template $$\mathbf{y}$$ using a user-specific transformation function $${T}_{K}$$, such that $$\mathbf{y}={T}_{K}\left(\mathbf{x}\right)$$, where $$K$$ is a secret key. When a template is compromised, a new unlinkable template can be generated by altering the key, i.e., $${\mathbf{y}}^{\mathrm{\prime}}={T}_{{K}^{\mathrm{\prime}}}\left(\mathbf{x}\right)$$ with $${K}^{\mathrm{\prime}}\ne K$$. This approach ensures cancelability, non-invertibility, diversity, and matching accuracy: the original biometric cannot be feasibly recovered from $$\mathbf{y}$$; different keys produce distinct templates for the same biometric input, i.e., $${T}_{{K}_{1}}\left(\mathbf{x}\right)\ne {T}_{{K}_{2}}\left(\mathbf{x}\right)$$ for $${K}_{1}\ne {K}_{2}$$; and the transformation preserves recognition performance within the transformed domain [4,7].
3.3. Physically Unclonable Function
Physical Unclonable Function (PUF) are a hardware security technology based on the physical characteristics of a device. PUF comes from the IC manufacturing process, which adds random physical changes to the IC’s microstructure, making it unique and impossible to clone [24]. The core concept of PUF is CRP: a random string is input, and the PUF generates a unique response. PUFs are unpredictable but easy to build and check, making them suitable for security protection in lightweight devices. Since the output of a PUF is physically dependent, any tampering will alter its behavior, making it useless. These features enable PUF to be used as a cancelable step or as an authentication factor, increasing system complexity and improving security at the physical level [20].
4. Proposed Scheme
Table 2 lists the important symbols used to describe the proposed scheme. In the proposed scheme, the user’s fingerprint is captured and extracted by the device for local authentication, and cancelable biometric methods are used to avoid the risk of permanent leakage of biometric information. Currently, most mobile devices can be equipped with biometric scanners, which can easily scan the user’s fingerprint onto the device, thus solving the problem of biometric acquisition in the proposed scheme.
Table 2. Description of the Symbol.
|
Notation |
Definition |
|---|---|
|
Ui |
A user |
|
CS |
Contorl server |
|
Dj |
Drone |
|
$${K}_{global}$$ |
The global key generated by CS |
|
$${ID}_{u}$$ |
User’s identity |
|
$${ID}_{cs}$$ |
CS’s identity |
|
$${ID}_{d}$$ |
Drone’s identity |
|
$${PW}_{u}$$ |
User’s password |
|
$$Bi$$ |
User’s biometric |
|
$$CB$$ |
Generating a cancelable biometric template |
|
$$PID$$ |
Pseudo identity |
|
$$C/\mathrm{R}$$ |
PUF’s Challenge-Response Pair |
|
$${E}_{K}\left(\cdot\right)$$ |
Symmetric encryption |
|
$${D}_{K}\left(\cdot \right)$$ |
Symmetric decryption |
|
$$\mathrm{N}$$ |
Random numbers |
|
$$⨁$$ |
Bitwise XOR operator |
|
$$\parallel$$ |
Concatenation operator |
4.1. Cancelable Biometric Template
Figure 2 illustrates the integration of the cancelable biometric mechanism with FE and PUF. The raw fingerprint vector is transformed into a cancelable version $$\mathbf{y}={T}_{K}\left(\mathbf{x}\right)$$, which is further processed through FE.Gen(·) to obtain auxiliary data $$\sigma$$, and used as input to the PUF for generating the response R. We propose an FFT-GRP-based method to improve efficiency and robustness.
The transformation parameters (non-repeating random permutation array r, n p×q-dimensional Gaussian Random Projection (GRP) matrices) adopt a design of dynamic generation and no local persistent storage to completely avoid the risk of parameter storage leakage. The specific implementation is as follows:
- (1)
-
Seed Generation: After the user enters the password $${PW}_{u}$$, the local device invokes its own dedicated PUF, and combines the user-specific salt $${Salt}_{u}$$ synchronized from the server, and generates a cryptographically secure seed through XOR operation and PUF mapping. The formula is $$Seed={PUF}_{u}\left({PW}_{u}\oplus {Salt}_{u}\right)$$. This seed integrates the secrecy of the password, the physical uniqueness of the PUF, and the randomness of the salt, and attackers cannot restore the seed with only a single element.
- (2)
-
Deterministic Parameter Generation: The $$Seed$$ is used as the initial input of the CSPRNG (Cryptographically secure pseudorandom number generator), ensuring the consistency and uniqueness of the generation results. Random permutation array r composed of non-repeating integers is generated iteratively, and elements following a Gaussian distribution with a mean of 0 and a variance of 1/p (p is the matrix dimension) are generated to construct n $$p×q$$-dimensional GRP matrices.
- (3)
-
No-Storage Strategy: The generated r and GRP matrices only reside temporarily in the device memory to complete current FFT permutation, GRP transformation, and template matching operations. After the operations are completed, the temporary parameters in the memory are immediately destroyed, and no form of persistent storage (including plaintext, encrypted files, or hidden storage) is performed locally. The Control Server (CS) only stores the user’s pseudo-identity $${PID}_{u}$$, unique salt $${Salt}_{u}$$, CRPs, and does not store any information directly related to transformation parameters, further reducing the risk of centralized leakage.
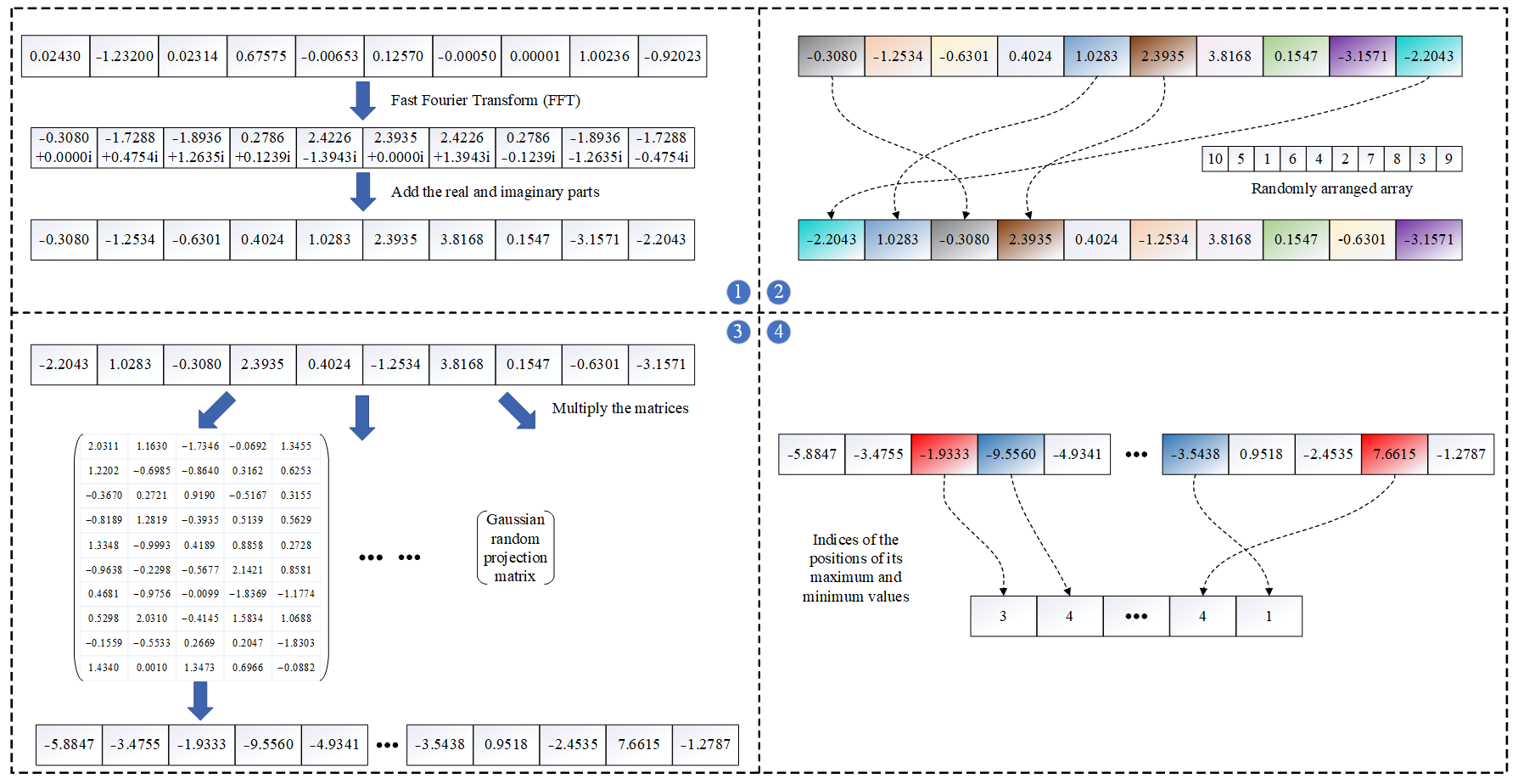
4.2. FFT-GRP
Although IoM is classic and efficient, Ghammam et al. [25] pointed out that IoM is not as resistant to various attacks as initially claimed, and the scheme is very susceptible to authentication and linking attacks. GRP-based IoM hashing [10] embeds the fingerprint vector into an n-dimensional Gaussian random subspace and extracts the index of the maximum projection feature. From the perspective of Locality Sensitive Hashing (LSH), this is equivalent to a hashing entry in the rank space [26]. The FFT-GRP method we propose combines GRP, Fast Fourier Transform, and random arrange to improve the efficiency and accuracy of fingerprint recognition.
GRP-based IoM hashing embeds the fingerprint vector into an n-dimensional Gaussian random subspace and extracts the index of the maximum projection feature. From the perspective of Locality Sensitive Hashing (LSH), this is equivalent to a hashing entry in the rank space [25]. Our method adopts this concept to enhance the efficiency and accuracy of fingerprint recognition. The method we use to generate templates is based on GRP and combines it with the Fast Fourier Transform (FFT) and random arrangement, which we call FFT-GRP. The specific process is as Figure 3 follows:
- (1)
-
FFT transformation is performed on the original fingerprint x (length is 299 bits) to generate complex vectors and sum the actual part and imaginary part to obtain a new real-value string $$\bar{x}$$ (length still remains 299 bits).
- (2)
-
Rearrange vector $$\bar{x}$$ using a non-repeating random array $$r$$, where $$max\left(r\right)=length\left(r\right)=length\left(\bar{x}\right)$$. For each position i, set $$\widehat{x_i}=\bar{x}_{r_i}$$. For example, if $${r}_{1}$$ = 10, place the 10th element of $$\bar{x}$$ at the first position. In step 2, blocks of the same color are mapped vertically, changing their position indices while retaining their original values.
- (3)
-
Generate $$n$$ random Gaussian projection matrices of dimensions $$p×q$$. To facilitate matrix multiplication, it is required that $$p=length(\hat{x})$$. Multiply $$\hat{x}$$ with each of the $$n$$ matrices to obtain $$n$$ vectors of dimensions $$1×q$$, denoted as $${x}_{i}^{\prime}\left(i\in \left[1,n\right]\right)$$.
- (4)
-
For the obtained n vectors $${x}_{i}^{\prime}\left(i\in \left[1,n\right]\right)$$, record the index positions of their maximum and minimum values to generate a positional index vector of length 2n. In step 4, red blocks represent the maximum value blocks, and blue blocks represent the minimum value blocks; their position indices are mapped to the new sequence.
In our scheme, we first use the Fast Fourier Transform (FFT) to process the raw vector, converting fingerprint data from the spatial domain to the frequency domain. This makes the frequency characteristics of the fingerprint more pronounced, which is beneficial for subsequent processing. However, in practical applications, FFT is generally considered reversible. We then introduce random permutation and Gaussian Random Projections (GRP).
Unlike typical random projections, Gaussian random projection (GRP) matrices preserve the statistical structure and orthogonality of the original data. They enhance dimensionality reduction while maintaining discriminative features. The hash indices obtained from GRP also preserve Euclidean distance relations, which benefits template stability and matching performance [10].
4.3. User Registration Phase
In this phase, the user registers with the control server and obtains essential parameters for subsequent authentication.
Step-1: The user sends a registration request Regreq to CS.
Step-2: Upon receiving the request, CS generates a challenge $${C}_{u}$$ and global key $${K}_{global}$$, then returns $${C}_{u}$$ to the user.
Step-3: The user’s device computes $${R}_{u}={PUF}_{u}\left({C}_{u}\right)$$, inputs $${ID}_{u},{PW}_{u}$$, and biometric $${Bi}_{u}$$. Using the cancelable transformation (Figure 3), it computes $${Bi}_{u}^{*}=CB\left({Bi}_{u}\right)$$ and derives ($${\sigma }_{i}$$, $${\tau }_{i}$$) = Gen($${Bi}_{u}^{*}$$). Then, it computes $${R}_{{\sigma }_{i}}=PUF\left({\sigma }_{i}\right)$$ and $$RPW=h\left({ID}_{u}||{PW}_{u}||{R}_{{\sigma }_{i}}\right)$$. The tuple ($${R}_{u}$$,$${ID}_{u}$$,$$RPW$$) is sent to CS.
Step-4: CS computes a pseudo-identity $${PID}_{u}={ID}_{u}\oplus h\left({K}_{global}||{ID}_{cs}\right)$$ and $$={PID}_{u}\oplus h\left({ID}_{u}||RPW\right)$$. It stores $$\left({PID}_{u},\left({C}_{u},{R}_{u}\right)\right)$$ for future authentication and replies with $$\left({ID}_{cs},A\right)$$.
Step-5: The user calculates $${ID}_{cs}^{\mathrm{\prime}}={ID}_{cs}\oplus {R}_{{\sigma }_{i}}$$ and stores $$\left(A,{ID}_{cs}^{\mathrm{\prime}},RPW,{\mathrm{\tau }}_{i}\right)$$ in the smart card (SC).
4.4. Drones Registration Phase
Before deploying a new drone, you need to register with CS, and the specific steps are as follows.
Step-1: The drone sends a registration request to CS, where $${Reg}_{req}$$ represents the registration request.
Step-2: CS first generates an ID for the drone, denoted as $${ID}_{d}$$, and a challenge $${C}_{d}$$ for the authentication process. CS calculates a pseudo identity for the drone $${PID}_{d}={ID}_{d}\oplus h\left({K}_{global}||{ID}_{cs}\right)$$. The data $$\left({PID}_{d},{C}_{d}\right)$$ is sent to the drone.
Step-3: The drone uses $${C}_{d}$$ as input for its PUF and obtains the response $${R}_{d}={PUF}_{d}\left({C}_{d}\right)$$. The drone stores $${PID}_{d}$$ in its device and sends $${R}_{d}$$ back to CS.
Step-4: CS stores the data $$(ID_d,PID_d,(C_d,R_d))$$ in the server.
4.5. Authentication Phase
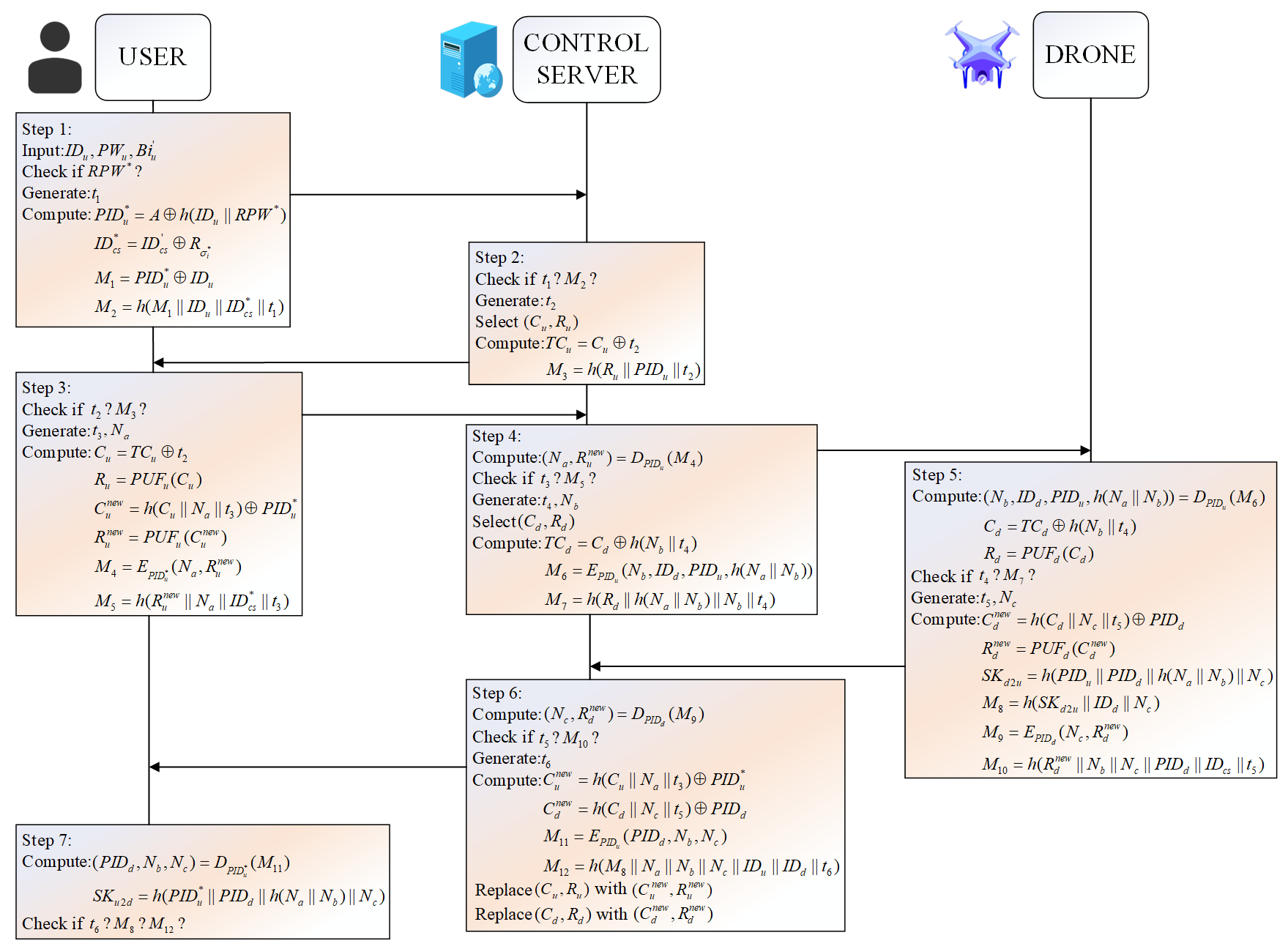
After registration, the user uses the smart card to authenticate with the control server and drone. Figure 4 summarizes the protocol.
Step-1: The user inserts the smart card, inputs $$\left({ID}_{u}{,PW}_{u}\right)$$, and captures biometric $${Bi}_{u}$$. The device computes the cancelable template $${Bi}_{u}^{*}=CB\left({Bi}_{u}\right)$$, then recovers $${\sigma }_{i}^{*}=Rep\left({\tau }_{i},{Bi}_{u}^{*}\right)$$ and obtains $${R}_{{\sigma }_{i}^{*}}=PUF\left({\sigma }_{i}^{*}\right)$$. It computes $${RPW}^{*}$$ and compares with stored RPW. If matched, the user calculates $${PID}_{u}^{*}$$ and $${ID}_{cs}^{*}$$, then generates timestamp $${t}_{1}$$, and computes $${M}_{1}={\mathrm{P}\mathrm{I}\mathrm{D}}_{\mathrm{u}}^{\mathrm{*}}\oplus {ID}_{u}$$ and $${M}_{2}=h\left({M}_{1}||{ID}_{u}||{ID}_{cs}^{*}||{t}_{1}\right)$$. The message $$\left({M}_{1},{M}_{2},{t}_{1}\right)$$ is sent to CS via a public channel.
Step-2: CS checks if $${t}_{1}$$ is fresh. If valid, it uses stored $${PID}_{u}$$ to recover $${ID}_{u}={PID}_{u}\oplus {M}_{1}$$ and verifies $${M}_{2}$$. Then, it selects $$\left({C}_{u},{R}_{u}\right)$$ based on $${ID}_{u}$$, generates $${t}_{2}$$, computes $${TC}_{u}$$ and $${M}_{3}$$, and sends ($${M}_{3}$$,$${TC}_{u}$$,$${t}_{2}$$) to the user.
Step-3: The user validates $${t}_{2}$$, derives $${C}_{u}$$=$${TC}_{u}\oplus {t}_{2}$$, and obtains $${R}_{u}={PUF}_{u}\left({C}_{u}\right)$$. If matched with the original, it verifies $${M}_{3}$$, then generates $${t}_{3}$$ and random $${N}_{a}$$, and computes $${C}_{u}^{new}=h\left({C}_{u}||{N}_{a}||{t}_{3}\right)\oplus {PID}_{u}^{*},{R}_{u}^{new}={PUF}_{u}\left({C}_{u}^{new}\right)$$. The user encrypts $${M}_{4}={E}_{{PID}_{u}^{*}}\left({N}_{b},{R}_{u}^{new}\right)$$ , calculates $${M}_{5}=h\left({R}_{u}^{new}||{N}_{a}||{ID}_{cs}^{*}||{t}_{3}\right)$$, and sends ($${M}_{4}$$,$${M}_{5}{,t}_{3}$$) to CS.
Step-4: CS checks $${t}_{3}$$, decrypts $$M$$ using $${PID}_{u}$$ to recover $$\left({N}_{a},{R}_{u}^{new}\right)$$, and verifies $${M}_{5}$$. If valid, it generates $${t}_{4}$$ and random $${N}_{b}$$, selects $$\left({C}_{d},{R}_{d}\right)$$, and computes $${TC}_{d}={C}_{d}\oplus h\left({N}_{b}||{t}_{4}\right)$$, $${M}_{6}={E}_{{PID}_{d}}\left({N}_{b},{ID}_{d},{PID}_{u},h\left({N}_{a}||{N}_{b}\right)\right)$$, and $${M}_{7}=\mathrm{ }h\left({R}_{d}||h\left({N}_{a}||{N}_{b}\right)||{N}_{b}||{t}_{4}\right)$$. Then $$\left({M}_{6},{M}_{7},{TC}_{d},{t}_{4}\right)$$ is sent to the drone.
Step-5: The drone validates $${t}_{4}$$, decrypts $${M}_{6}$$, derives $${C}_{d}$$, and obtains $${R}_{d}={PUF}_{d}\left({C}_{d}\right)$$. After verifying $${M}_{7}$$, it generates $${t}_{5}$$ and random $${N}_{c}$$, computes $${C}_{d}^{new}=h\left({C}_{d}||{N}_{c}||{t}_{5}\right)\oplus {PID}_{d}$$, and $${R}_{d}^{new}={PUF}_{d}\left({C}_{d}^{new}\right)$$. It then calculates the session key $${SK}_{d2u}=h\left({PID}_{u}||{PID}_{d}||h\left({N}_{a}||{N}_{b}\right)||{N}_{c}\right)$$, encrypts $${M}_{9}={E}_{{PID}_{d}}\left({N}_{c},{R}_{d}^{new}\right)$$, and computes $${M}_{8}$$ and $${M}_{10}$$. The tuple ($${M}_{8}$$,$${M}_{9}$$,$${M}_{10}$$,$${t}_{5}$$) is sent to CS.
Step-6: CS checks $${t}_{5}$$, decrypts $${M}_{9}$$ to get $$\left({N}_{c},{R}_{d}^{new}\right)$$, and verifies $${M}_{10}$$. It then computes $${C}_{u}^{new}$$ and $${C}_{d}^{new}$$, updating the stored $$\left({C}_{u},{R}_{u}\right)$$ and $$\left({C}_{d},{R}_{d}\right)$$ to their new values. It generates $${t}_{6}$$, prepares $${M}_{11}={E}_{{PID}_{u}}\left({PID}_{d},{N}_{b},{N}_{c}\right)$$, $${M}_{12}=h\left({M}_{8}||{N}_{a}||{N}_{b}||{N}_{c}||{ID}_{u}||{ID}_{d}||{t}_{6}\right)$$, then sends $$\left({M}_{11},{M}_{12},{t}_{6}\right)$$ to the user.
Step-7: The user decrypts $${M}_{11}$$ to retrieve $$\left({PID}_{d},{N}_{b},{N}_{c}\right)$$ and calculates $${SK}_{u2d}=h\left({PID}_{u}^{\mathrm{*}}||{PID}_{d}||h\left({N}_{a}||{N}_{b}\right)||{N}_{c}\right)$$ and $${ID}_{d}={PID}_{d}\oplus \left({PID}_{u}^{\mathrm{*}}\oplus {ID}_{u}\right)$$. If $${M}_{8}$$ and $${M}_{12}$$ are both valid, then all parties have authenticated each other and agreed on the session key $${SK}_{u2d}={SK}_{d2\mathrm{u}}$$.
4.6. Password/Biometrics Update Phase
To address template leakage or proactive privacy protection needs, this scheme designs a lightweight cancelable process based on the dynamic parameter generation mechanism. Template invalidation can be achieved only by updating the password or salt without modifying the user’s original biometrics. The specific steps are as follows:
- (1)
-
The user enters a valid $${ID}_{u},{PW}_{u},{Bi}_{u}^{\mathrm{\prime}}$$, and calculates $${Bi}_{u}^{\mathrm{\prime}\mathrm{\prime}}=CB\left({Bi}_{u}^{\mathrm{\prime}}\right)$$; $${\sigma }_{i}^{\mathrm{*}}=Rep\left({Bi}_{u}^{\mathrm{\prime}\mathrm{\prime}},{\mathrm{\tau }}_{i}\right)$$; $${RPW}^{\mathrm{*}}=h\left({ID}_{u}||{PW}_{u}||{\sigma }_{i}^{\mathrm{*}}\right)$$. If the calculated $${RPW}^{\mathrm{*}}$$ does not match the RPW stored in the SC, the process is terminated. If they are the same, the user sends a template revocation request to the CS, including their own pseudo-identity $${PID}_{u}$$ and a fresh timestamp to prevent request replay attacks.
- (2)
-
After receiving the request, the CS verifies the validity of $${PID}_{u}$$ through pre-stored user authentication information and checks the freshness of the timestamp. If the verification passes, the user is allowed to perform the update operation.
- (3)
-
The user can choose two update methods: ① Password update: Enter a new password $${PW}_{u}^{new}$$ to generate a new seed $${Seed}^{new}={PUF}_{u}\left({PW}_{u}^{new}\oplus {Salt}_{u}\right)$$; ② Salt update with retained password: The CS generates a new salt $${Salt}_{u}^{new}$$ and synchronizes it to the user’s device, generating a new seed $${Seed}^{new}={PUF}_{u}\left({PW}_{u}\oplus {Salt}_{u}^{new}\right)$$. The new seed generates a brand-new permutation array and GRP matrix through CSPRNG, and a new cancelable biometric template is generated based on the new parameters.
- (4)
-
Template Synchronization and Old Template Invalidation: The user’s device synchronizes the CRP corresponding to the new template to the CS. The CS updates the stored user authentication information, associates $${PID}_{u}$$ with the new template CRP, and permanently invalidates the old template corresponding to the old password/old salt. The old template cannot be restored through the new parameters, and even if leaked, it cannot be used for subsequent authentication, achieving efficient and secure revocability.
4.7. Drones Performs Self-Checks/Forms a Swarm
The process uses PUF (Physical Unclonable Function) hardware uniqueness, random number challenges, and hash verification to confirm the drone’s legitimacy. Drones perform a self-check either on a schedule or before joining the swarm with the server. The following is the self-check process.
- (1)
-
CS generates a random number $${N}_{a}$$ and retrieves the drone’s $${PID}_{d}$$ and initial challenge $${C}_{d}$$. Calculate encrypted data $${PID}_{d}^{*}={PID}_{d}\oplus {N}_{a},{N}_{a}^{*}={N}_{a}\oplus {R}_{d}$$, $${R}_{d}$$ is initial PUF response, known only to CS and the drone. $${M}_{1}=h\left({N}_{a}|\left|{R}_{d}\right||{PID}_{d}\right)$$, CS sends the challenge message to the drone: ($${C}_{d}$$, $${M}_{1}$$, $${PID}_{d}^{*}$$, $${N}_{a}^{*}$$).
- (2)
-
The drone uses its PUF to compute $${{R}_{d}^{\prime}=PUF}_{d}\left({C}_{d}\right)$$. Decrypt to get key data $${N}_{a}$$ and $${PID}_{d}$$. Verify integrity $${M}_{1}^{\prime}=h\left({N}_{a}|\left|{R}_{d}^{\prime}\right||{PID}_{d}\right)$$. If $${M}_{1}^{\prime}\ne {M}_{1}$$, reject the request. Generate drone-side random number $${N}_{b}$$ and calculate ($${\sigma }_{i}$$, $${\tau }_{i}$$) = Gen$$\left({PID}_{d}\right)$$, $${\tau }_{i}^{\prime}={N}_{b}\oplus {\tau }_{i}$$, $${N}_{b}^{*}={N}_{b}\oplus {R}_{d}^{\prime}$$, $${M}_{2}=h\left({\sigma }_{i}||{N}_{b}\right)$$. The drone sends the response message ($${\tau }_{i}^{\prime}$$, $${N}_{b}^{*}$$, $${M}_{2}$$) to CS.
- (3)
-
CS decrypts $${N}_{b}={N}_{b}^{*}\oplus {R}_{d}$$, $${\tau }_{i}={N}_{b}\oplus {\tau }_{i}^{\prime}$$. Verify key $${\sigma }_{i}$$: $${\sigma }_{i}^{*}=Rep\left({\tau }_{i},{PID}_{d}\right)$$. Check if $${M}_{2}$$, if verification passes, update the drone’s pseudo-identity $${PID}_{d}^{new}$$. Generate a cluster session key: $$\mathrm{S}\mathrm{K}=\mathrm{h}\left({\tau }_{i}|\left|{N}_{a}\right||{N}_{b}||{R}_{d}\right)$$ for future communication. If verification fails, add the drone to the blacklist and block network access.
The core logic of drone swarm hierarchical authentication is that users only complete mutual authentication with the swarm Leader once, and ordinary drones, after passing self-check, access the swarm via “Control Server (CS) authentication + Leader authentication” without interacting with users to reduce redundant overhead, thereby reducing redundant overhead and effectively intercepting malicious drones.
- (1)
-
Ordinary drone sends a join request: Sends $${Req}_{join}=\left\{{PID}_{d}^{new},{t}_{join}\right\}$$ to CS; CS verifies timestamp freshness and whether $${PID}_{d}^{new}$$ is in the self-check-passed list.
- (2)
-
CS authenticates & issues a credential: CS generates temporary challenge $${C}_{temp}$$ and access credential $$\mathrm{C}\mathrm{e}\mathrm{r}\mathrm{t}=\mathrm{h}\left({PID}_{leader}||{PID}_{d}^{new}||{K}_{global}\right)$$, sends $${M}_{1}=\left({PID}_{leader},{C}_{temp},\mathrm{C}\mathrm{e}\mathrm{r}\mathrm{t},{t}_{cs}\right)$$ to ordinary drone; ordinary drone verifies $${t}_{cs}$$ and $$\mathrm{C}\mathrm{e}\mathrm{r}\mathrm{t}$$ integrity.
- (3)
-
Leader authenticates & grants access: Ordinary drone sends $${M}_{2}=\left({PID}_{d}^{new},{ R}_{temp}, \mathrm{C}\mathrm{e}\mathrm{r}\mathrm{t},{t}_{rd}\right),{R}_{temp}={\mathrm{P}\mathrm{U}\mathrm{F}}_{d}\left({C}_{temp}\right)$$ to leader; leader verifies $${t}_{rd}$$ and $$\mathrm{C}\mathrm{e}\mathrm{r}\mathrm{t}$$, synchronizes $$\left({C}_{temp},{R}_{temp}\right)$$ to CS for PUF validity check; if passed, Leader generates cluster session key $${SK}_{group}$$, encrypts and sends it, and synchronizes CS to update the swarm list.
5. Security Analysis of the Proposed Scheme
This section presents both formal and informal analyses, evaluating potential attacks using the ROR model and AVISPA tool.
5.1. Formal Analysis Under Real-or-Random (ROR) Model
In this section, we will introduce the use of the widely used ROR model [21] to prove the semantic security of the protocol. Table 3 shows the definition of the symbols and their query bounds.
Table 3. Description of the symbol.
|
Parameters |
Definition |
Query Bounds |
|---|---|---|
|
```latex\mathcal{A}``` |
Polynomial-time adversary attacking Protocol $$\mathcal{P}$$ in the random oracle model |
-- |
|
```latexl``` |
Bit length of the biometric feature $${Bi}_{i}$$ |
Corresponding to the dimension of the fingerprint feature vector (Section 4.1) |
|
```latex{q}_{h}``` |
Upper bound of Hash Oracle queries. |
Covers all calls to $$h\left( \right)$$ (e.g., $$RPW$$, $$M_2/M_3/M_5/PID_u/PID_d/SK$$) generation; $${q}_{h}\le poly\left(n\right)$$ |
|
```latex{q}_{P}``` |
Upper bound of PUF Oracle queries. |
Covers $${PUF}_{u}\left( \right)$$ (generating $${R}_{u}$$,$$\,{R}_{u}^{new}$$) and $${PUF}_{d}\left( \right)$$ (generating $${R}_{d}$$,$$\,\mathrm{ }{R}_{d}^{new}$$); $${q}_{P}\le poly\left(n\right)$$ |
|
```latex{q}_{s}``` |
Upper bound of Send Oracle queries |
Covers interception/forgery/modification of public-channel messages; $${q}_{s}\le poly\left(n\right)$$ |
|
```latex|RH|``` |
Size of the hash function output domain |
Determined by hash output bit length (e.g., 256 bits for SHA-256) |
|
```latex|RP|``` |
Size of the PUF response domain |
Determined by PUF hardware implementation in resource-constrained devices |
|
```latex|DC|``` |
Size of the password dictionary for guessing attacks |
Consistent with the Adversary Model (Section 2.2) |
Security Proof: The security proof provided in Theorem 1 is similar to the security proof given in [21,22].
Theorem 1. Let $$\mathcal{A}$$ be a polynomial-time adversary attacking protocol $$\mathcal{P}$$ in the random oracle model. Table 3 definitions of parameters and query bounds. Then:
|
```latex{Adv}_{p}\left(A\right)\le \frac{{q}_{h}^{2}}{|RH|}+\frac{{q}_{P}^{2}}{|RP|}+\frac{{q}_{s}}{{2}^{l-1}\cdot |DC|}``` |
(1) |
Proof. Five games, denoted as $${\mathrm{G}}_{i}\left(i = 0,\mathrm{ }1,\mathrm{ }2,\mathrm{ }3,\mathrm{ }4\right)$$ are defined. Let $${Succ}_{i}$$ represent the event that the attacker $$\mathcal{A}$$ successfully guesses the bit c in game $${\mathrm{G}}_{i}$$. □
G0: Fully simulates the real execution of Protocol $$\mathcal{P}$$. Hash operations, PUF responses, fuzzy extractor (FE) operations, and timestamp verification are performed in accordance with the original protocol logic. The adversary’s advantage is defined as:
|
```latex{adv}_{\mathcal{P}}\left(\mathcal{A}\right)=|2\cdot Pr\left[{Succ}_{0}\right]-1|``` |
(2) |
G1: In G1, the attacker performs an eavesdropping attack on $$\mathcal{P}$$. $$\mathcal{A}$$ can intercept authentication phase messages like $$\left({M}_{1},{M}_{2},{t}_{1}\right)$$, etc. In this game, $$\mathcal{A}$$ makes an Execute($${\varPi }^{t},{\varPi }^{u}$$) (intercept public channel messages such as $$\left({M}_{1},{M}_{2},{t}_{1}\right)$$) and a Test query (verify whether the session key is random) to verify whether it is the true session key SK or a random number. The session key SK is calculated as: $$SK=h\left({ID}_{u}||{PID}_{RD}||{ID}_{RD}||h\left({N}_{b}||{N}_{c}\right)||{N}_{d}\right)$$. But this $$SK$$ isn’t on the public channel, and relies on random numbers and encrypted pseudo-identities ($${PID}_{u}={ID}_{u}\oplus h\left({K}_{global}||{ID}_{cs}\right)$$). So $$\mathcal{A}$$ can’t get or derive $$SK$$. Associated Components: One-wayness of the hash function h(·), encrypted pseudo-identity mechanism. Therefore, the probability of $$\mathcal{A}$$ winning G1 by eavesdropping on the exchange messages does not increase. That is to say,
|
```latexPr[Succ_1]=Pr[Succ_0]``` |
(3) |
G2: On the basis of G1, simulate Hash Oracle responses—all h(·) queries from the adversary return random values conforming to the hash distribution. Transition Argument: According to the birthday paradox, the upper bound of the hash collision probability is $$\frac{{q}_{h}^{2}}{2|RH|}$$. Associated Components: Random oracle assumption of the hash function (used to generate RPW,$$\,{M}_{2},{M}_{3}$$, etc.). The random oracle property makes the simulated responses indistinguishable from real responses, as:
|
```latex|Pr\left[{Succ}_{2}\right]-Pr\left[{Succ}_{1}\right]|\le \frac{{q}_{h}^{2}}{2|RH|}``` |
(4) |
G3: On the basis of G2, simulate PUF Oracle responses-all PUF(·) queries from the adversary return random values conforming to the PUF distribution. But PUF has physical unclonability and pseudorandomness. Associated Components: PRF property of PUF (generating challenge-response pairs C/R). and its responses are indistinguishable from random numbers. The upper bound of the collision probability is $$\frac{{q}_{P}^{2}}{2|RP|}$$, as:
|
```latex|Pr\left[{Succ}_{3}\right]-Pr\left[{Succ}_{2}\right]|\le \frac{{q}_{P}^{2}}{2|RP|}``` |
(5) |
G4: In this game model, no random oracle is assumed. The probability of $$\mathcal{A}$$ successfully forging all messages depends on the inclusion of CorruptDevice operations. In this scenario, $$\mathcal{A}$$ can retrieve all secret data stored in the user’s device ($$\mathrm{A},{ID}_{\mathrm{C}\mathrm{S}},RPW,{\mathrm{\tau }}_{i}$$). However, $$\mathcal{A}$$ cannot derive any valuable information from this data, as the user’s ID, password, and biometric features are not directly stored on the smart card. Instead, the card stores data computed from these elements. $$RPW=h\left({ID}_{u}||{PW}_{u}||{R}_{{\sigma }_{i}}\right)$$ relies on $${R}_{{\sigma }_{i}}$$ generated by FE and PUF. Assuming the scheme replaces the original mechanism with k random bits, the probability of guessing the biometric password approximates $$\frac{1}{{2}^{k}}$$. The adversary needs to guess both the password (from DC) and the biometric (length k), with a success probability upper bound of $$\frac{{q}_{s}}{{2}^{k}\cdot |DC|}$$.The system also limits the number of incorrect password attempts. Since games G3 and G4 remain identical under scenarios without guessing attacks, we derive:
|
```latex|Pr\left[{Succ}_{4}\right]-Pr\left[{Succ}_{3}\right]|\le \frac{{q}_{s}}{{2}^{k}\cdot |DC|}``` |
(6) |
Note that the session keys for all random oracles are simulated in game G4. So after the Test query is completed, $$\mathcal{A}$$ needs to guess bit c to win the game. We infer that:
|
```latexPr\left[{Succ}_{4}\right]=\frac{1}{2}``` |
(7) |
Based on (1), (2), and (6), we can first derive the following relationship:
|
```latex\frac{1}{2}{adv}_{\mathcal{P}}\left(\mathcal{A}\right)=|Pr\left[{Succ}_{0}\right]-\frac{1}{2}|=|Pr\left[{Succ}_{1}\right]-\frac{1}{2}|= |Pr\left[{Succ}_{1}\right]-Pr\left[{Succ}_{4}\right]|``` |
(8) |
Using the triangular inequality and (6), we further derive:
|
```latex\begin{aligned}|Pr[Succ_1]-\frac{1}{2}|&=|Pr[Succ_1]-Pr[Succ_4]|\\&\leq|Pr[Succ_1]-Pr[Succ_3]|+|Pr[Succ_3]-Pr[Succ_4]|\\&\leq|Pr[Succ_1]-Pr[Succ_2]|+|Pr[Succ_2]-Pr[Succ_3]|\\&\,\,\,\,\,\,\,\,\,\,\,\,\,\,\,\,\,\,\,\,\,\,\,\,\,\,\,\,\,\,\,\,\,\,\,\,+|Pr[Succ_3]-Pr[Succ_4]|\end{aligned}```
|
(9) |
Based on (3), (4), and (5), we can deduce:
|
```latex|Pr\left[{Succ}_{1}\right]-\frac{1}{2}|=|Pr\left[{Succ}_{1}\right]-Pr\left[{Succ}_{4}\right]|\le \frac{{q}_{h}^{2}}{2|RH|}+\frac{{q}_{P}^{2}}{2|RP|}+\frac{{q}_{s}}{{2}^{k}\cdot |DC|}``` |
(10) |
Thus:
|
```latex\frac{1}{2}{adv}_{\mathcal{P}}\left(\mathcal{A}\right)\le \frac{{q}_{h}^{2}}{2|RH|}+\frac{{q}_{P}^{2}}{2|RP|}+\frac{{q}_{s}}{{2}^{k}\cdot |DC|}``` |
(11) |
In conclusion, this result demonstrates that the proposed scheme achieves session key security:
|
```latex{adv}_{\mathcal{P}}\left(\mathcal{A}\right)\le \frac{{q}_{h}^{2}}{|RH|}+\frac{{q}_{P}^{2}}{|RP|}+\frac{{q}_{s}}{{2}^{l-1}\cdot|DC|}``` |
(12) |
The security of the protocol relies on the synergy of four core components, which support the corresponding game transitions respectively:
- (1)
-
Hash Function h(·): Acts as a random oracle to generate message authentication codes, pseudo-identities, and session keys, supporting the transition from G1 to G2 and resisting hash collision attacks;
- (2)
-
PUF/PRF: The physical unclonability and pseudorandomness of PUF ensure the security of C/R pairs, supporting the transition from G2 to G3 and resisting PUF response forgery attacks;
- (3)
-
FE/Rep: The noise resistance of the Fuzzy Extractor ensures the matching accuracy of biometric templates. Combined with PUF, it generates $${R}_{{\sigma }_{i}}$$, supporting the transition from G3 to G4 and resisting biometric guessing attacks;
- (4)
-
Timestamps $${t}_{1}$$–$${t}_{6}$$: Prevent replay attacks through freshness verification, avoid the adversary interfering with game execution, and ensure the validity of all transitions.
5.2. Formal Analysis under Avispa Tool
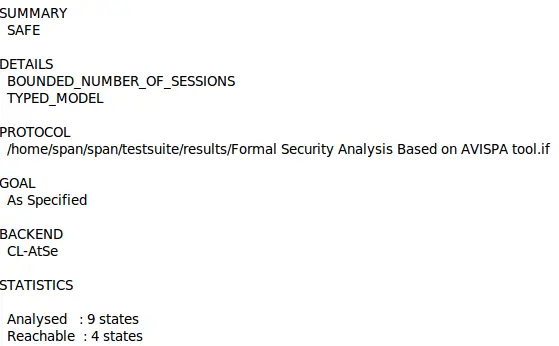
We use the AVISPA tool [27] to formally verify the security of the proposed protocol. AVISPA simulates against active threats, including replay and man-in-the-middle attacks, using the Dolev–Yao (DY) model [23]. The protocol is first written in High-Level Protocol Specification Language (HLPSL), then translated to Intermediate Format (IF) via the HLPSL2IF converter, and finally analyzed using AVISPA’s backends. The Output Format (OF) clearly states whether an attack is possible. The intruder model actively participates in sessions. As shown in Figure 5 simulation under the SPAN interface confirms that the proposed protocol resists both replay and man-in-the-middle attacks.
5.3. Informal Analysis
We believe users’ mobile devices and drones are vulnerable, with stored data at risk of theft. Data is transmitted via public channels, making it easy to intercept. However, we consider this protocol safe and capable of achieving the following objectives. Table 4 shows the comparison of the proposed scheme with other schemes in the field in terms of their resistance to different attacks. Where “ √ ” indicates that it can be done, “ × ” indicates that it cannot be done, and “NA” indicates discussion or ambiguity.Each claimed security property is mapped to the adversary’s capabilities (from Section 2.2) and the corresponding protocol steps that ensure the property, as follows:
- (1)
- A1 (User Anonymity):
The corresponding threat is ID disclosure via public channel interception, and the adversary’s capability is II.B.1 (public channel interception). The protocol ensures this property through the following steps: During user registration, $${PID}_{u}={ID}_{u}\oplus h\left({K}_{global}||{ID}_{cs}\right)$$ is executed (Step 4); during authentication, the real ID is hidden via $${M}_{1}={\mathrm{P}\mathrm{I}\mathrm{D}}_{u}^{\mathrm{*}}\oplus {ID}_{u}$$ (Step 1), and only the Control Server (CS) can recover $${ID}_{u}$$ in Step 2, preventing ID leakage over public channels.
- (2)
- A2 (Forward Secrecy):
The corresponding threat is the compromise of long-term keys/CRPs, and the adversary’s capabilities are II.B.2 (drone memory compromise) and II.B.3 (partial parameter leakage). The protocol’s guarantee steps include: After authentication, CRP updates are performed, i.e., $${C}_{u}^{new}=h\left({C}_{u}||{N}_{a}||{t}_{3}\right)\oplus {PID}_{u}^{*}$$ and $${C}_{d}^{new}=h\left({C}_{d}||{N}_{c}||{t}_{5}\right)\oplus {PID}_{d}$$ (Steps 3, 5), and the Control Server updates the stored $$\left({C}_{u},{R}_{u}\right)$$ and $$\left({C}_{d},{R}_{d}\right)$$ in Step 6, ensuring that even if long-term keys or old CRPs are compromised, past session keys remain secure.
- (3)
- A3 (Sensor Anonymity):
The corresponding threat is drone ID disclosure, and the adversary’s capability is II.B.1 (public channel interception). The protocol generates a pseudo-identity via $${PID}_{d}={ID}_{d}\oplus h\left({K}_{global}||{ID}_{cs}\right)$$ during drone registration (Step 2) and hides $${ID}_{d}$$ in the encrypted message $${M}_{6}$$ during authentication (Step 4), preventing the drone’s real ID from being intercepted and obtained.
- (4)
- A4 (Replay Attack Resistance):
The corresponding threat is the replay of authentication messages ($${M}_{1}$$–$${M}_{12}$$), and the adversary’s capability is II.B.1 (message replay). The protocol performs freshness checks on timestamps $${t}_{1}$$–$${t}_{6}$$ (Steps 2, 3, 4, 5, 6) and introduces random numbers $${N}_{a}/{N}_{b}/{N}_{c}$$ into session key calculation (Steps 3, 4, 5), ensuring that replayed old messages are rejected due to invalid timestamps or mismatched random numbers.
- (5)
- A5 (Man-in-the-Middle Attack Resistance):
The corresponding threat is message tampering/injection, and the adversary’s capability is II.B.1 (message modification/injection). The protocol verifies message integrity through a hash verification mechanism (e.g., $${M}_{2}=h\left({M}_{1}||{ID}_{u}||{ID}_{cs}^{*}||{t}_{1}\right)$$ (Step 1), $${M}_{3}=h\left({R}_{u}||{PID}_{u}||{t}_{2}\right)$$ (Step 2), etc.) and performs symmetric encryption on sensitive data $${M}_{4}={E}_{{PID}_{u}^{*}}\left({N}_{b},{R}_{u}^{new}\right)$$, $${M}_{6}={E}_{{PID}_{d}}\left({N}_{b},{ID}_{d},{PID}_{u},h\left({N}_{a}||{N}_{b}\right)\right)$$ to resist man-in-the-middle attacks on message tampering and injection.
- (6)
- A6 (Physical Attack Resistance):
The corresponding threat is Physical Unclonable Function (PUF) tampering/physical cloning, and the adversary’s capability is II.B.2 (drone memory compromise). The protocol leverages the unclonability of PUF—Challenge-Response Pairs (C,R) are bound to physical devices, and tampering invalidates PUF responses (Section 3.3)—while decoupling templates from physical biometrics via cancelable biometric transformation (FFT-GRP) (Section 4.2) to resist physical attacks on PUF and biometrics.
- (7)
- A7 (Device Loss Resilience):
The corresponding threat is smart card/drone loss with data extraction, and the adversary’s capability is II.B.2 (smart card/drone data extraction). The protocol ensures that smart cards only store derived data $$RPW=h\left({ID}_{u}||{PW}_{u}||{R}_{{\sigma }_{i}}\right)$$ instead of raw IDs, passwords, or biometrics (Step 3), and drones only store pseudo-identity $${PID}_{d}$$ without plaintext $${ID}_{d}$$ or global key $${K}_{global}$$ (Step 3), preventing sensitive information from being directly obtained if the device is lost.
- (8)
- A8 (Known Session Key Attack Resistance):
The corresponding threat is session key leakage leading to the compromise of past/future keys, and the adversary’s capability is II.B.1 (message interception). The protocol’s guarantee mechanisms include: The session key $$SK=h\left({PID}_{u}^{\mathrm{*}}||{PID}_{d}||h\left({N}_{a}||{N}_{b}\right)||{N}_{c}\right)$$ (Steps 5, 7) uses unique random numbers for each session, and Challenge-Response Pairs are updated after each authentication (Steps 3, 5, 6), ensuring that the leakage of a single session key does not affect the security of other sessions.
- (9)
- A9 (Password Guessing Attack Resistance):
The corresponding threat is online/offline password guessing via a dictionary, and the adversary’s capability is II.B.4 (guessing attacks). The protocol combines the password with biometric-derived $${R}_{{\sigma }_{i}}$$ to generate RPW ($$RPW=h\left({ID}_{u}||{PW}_{u}||{R}_{{\sigma }_{i}}\right)$$, Step 3) and limits the number of incorrect RPW matching attempts through the system (Section 4.6), significantly reducing the probability of successful password guessing.
- (10)
- A10 (User Device Loss Attack Resistance):
The corresponding threat is stolen devices leading to identity impersonation, and the adversary’s capability is II.B.2 (smart card data extraction). The protocol requires biometric verification during authentication, i.e., recovering $${\sigma }_{i}^{*}$$ via $${Bi}_{u}^{*}=CB\left({Bi}_{u}\right)$$ and $${\sigma }_{i}^{*}=Rep\left({\tau }_{i},{Bi}_{u}^{*}\right)$$ (Step 1), and the calculation of $${PID}_{u}$$ and $${ID}_{cs}$$ depends on valid RPW matching (Step 1). Even if smart card data is extracted, the adversary cannot complete impersonation due to the lack of biometrics.
- (11)
- A11 (Offline Attack Resistance):
The corresponding threat is offline brute-force attacks on intercepted encrypted messages, and the adversary’s capability is II.B.1 (message interception). The protocol uses pseudo-identities $$\left({PID}_{u},{PID}_{d}\right)$$ as keys for encrypted messages $$\left({M}_{4},{M}_{6},{M}_{9},{M}_{11}\right)$$ (Steps 3, 4, 5, 6), and pseudo-identities are derived from the global key$$\,{K}_{global}$$ unknown to the adversary, making offline cracking difficult without valid keys.
- (12)
- A12 (Sensor Theft Attack Resistance):
The corresponding threat is biometric template leakage due to stolen biometric sensors, and the adversary’s capability is II.B.2 (sensor data extraction). The protocol generates cancelable biometric templates (CB) via FFT-GRP transformation (Section 4.2), making it impossible to reverse the original biometric $${Bi}_{u}$$ from CB, and templates can be updated by modifying random permutation arrays $$r$$ or projection matrices, avoiding permanent biometric leakage after sensor theft.
- (13)
- A13 (Biometric Attack Resistance):
The corresponding threat is biometric template inversion/replay, and the adversary’s capability is II.B.3 (partial parameter leakage). The protocol prevents template inversion via $$CB = FFT-GRP\left({Bi}_{u}\right) + PUF\left({\sigma }_{i}^{*}\right)$$ (Section 4.1), and the $$Rep$$ function of the fuzzy extractor requires $${Bi}_{u}$$ to be sufficiently similar to the registered $${Bi}_{u}$$ ($$dis\left(Bi,{Bi}_{u}\right)<t$$, Section 4.1), resisting replayed forged biometric data.
- (14)
- A14 (Password/Biometric Update Support):
The corresponding threat is the inability to update credentials after compromise, and the adversary’s capability is II.B.2 (device data extraction). During the update phase, the protocol allows users to enter a new password ($${PW}_{u}^{new}$$) or new biometric ($${Bi}_{u}^{new}$$), calculate a new $${RPW}^{\mathrm{*}}=h\left({ID}_{u}||{PW}_{u}||{\sigma }_{i}^{\mathrm{*}}\right)$$ and replace the old RPW (Steps 1–2), enabling secure credential updates.
- (15)
- A15 (Mutual Authentication):
The corresponding threat is unilateral authentication failure, and the adversary’s capability is II.B.1 (impersonation via message forgery). The protocol ensures mutual authentication through three-level verification: Between the user and the Control Server via $${M}_{2}$$ (user to CS) and $${M}_{3}$$ (CS to user) (Steps 1–2), between the Control Server and the drone via $${M}_{7}$$ (CS to drone) and $${M}_{8}/{M}_{10}$$ (drone to CS) (Steps 4–5), and between the user and the drone via $${M}_{12}$$ (CS to user) and session key consistency check (Step 7), ensuring that the identities of all three parties are legally verified.
- (16)
- A16 (PUF Update Support):
The corresponding threat is stale Challenge-Response Pairs leading to PUF response forgery, and the adversary’s capability is II.B.2 (drone memory compromise). The protocol implements PUF updates by generating new Challenge-Response Pairs, i.e., $${C}_{u}^{new}=h\left({C}_{u}||{N}_{a}||{t}_{3}\right)\oplus {PID}_{u}^{*},{R}_{u}^{new}={PUF}_{u}\left({C}_{u}^{new}\right)$$ (Step 3), and $${C}_{d}^{new}=h\left({C}_{d}\left|\left|{N}_{c}\right|\right|{t}_{5}\right)\oplus {PID}_{d},{R}_{d}^{new}={PUF}_{d}\left({C}_{d}^{new}\right)$$ (Step 5), and the control server updates the stored $$\left({C}_{u},{R}_{u}\right)$$ and $$\left({C}_{d},{R}_{d}\right)$$ in Step 6, avoiding PUF response forgery using old CRPs.
- (17)
- A17 (Avispa-Verified Security):
The corresponding threats are replay/man-in-the-middle attacks, and the adversary’s capability is II.B.1 (message replay/injection). The protocol undergoes Avispa simulation via HLPSL specification (Section 5.2), and tool verification confirms its effective resistance to the aforementioned threats, ensuring the protocol’s security in simulated attack scenarios.
Table 4. Comparison of the Security Properties.
|
Scheme |
A1 |
A2 |
A3 |
A4 |
A5 |
A6 |
A7 |
A8 |
A9 |
A10 |
A11 |
A12 |
A13 |
A14 |
A15 |
A16 |
A17 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
|
[13] |
√ |
√ |
√ |
√ |
√ |
√ |
√ |
√ |
√ |
√ |
√ |
√ |
√ |
√ |
√ |
√ |
√ |
|
[17] |
√ |
√ |
NA |
√ |
√ |
√ |
√ |
× |
√ |
√ |
√ |
√ |
NA |
√ |
√ |
NA |
NA |
|
[18] |
√ |
√ |
√ |
√ |
√ |
√ |
√ |
× |
√ |
√ |
√ |
√ |
√ |
× |
√ |
√ |
√ |
|
[19] |
√ |
√ |
√ |
√ |
√ |
√ |
√ |
NA |
√ |
√ |
√ |
√ |
√ |
× |
√ |
× |
NA |
|
Ours |
√ |
√ |
√ |
√ |
√ |
√ |
√ |
√ |
√ |
√ |
√ |
√ |
√ |
√ |
√ |
√ |
√ |
A1: User Anonymity; A2: Forward Secrecy; A3: Sensor Anonymity; A4: Replay Attack; A5: Man-in-the-Middle Attack; A6: Physical Attack; A7: Device Loss Attack; A8: Known session Key attack; A9: Password Guessing Attack; A10: User Device Loss Attack; A11: Offline Attack; A12: Sensor Theft Attack; A13: Biometric Attack; A14: Password/Biometric update; A15: Mutual authentication; A16: PUF update; A17: Avispa.
6. Performance Analysis and Comparison
6.1. Accuracy Performance Evaluation
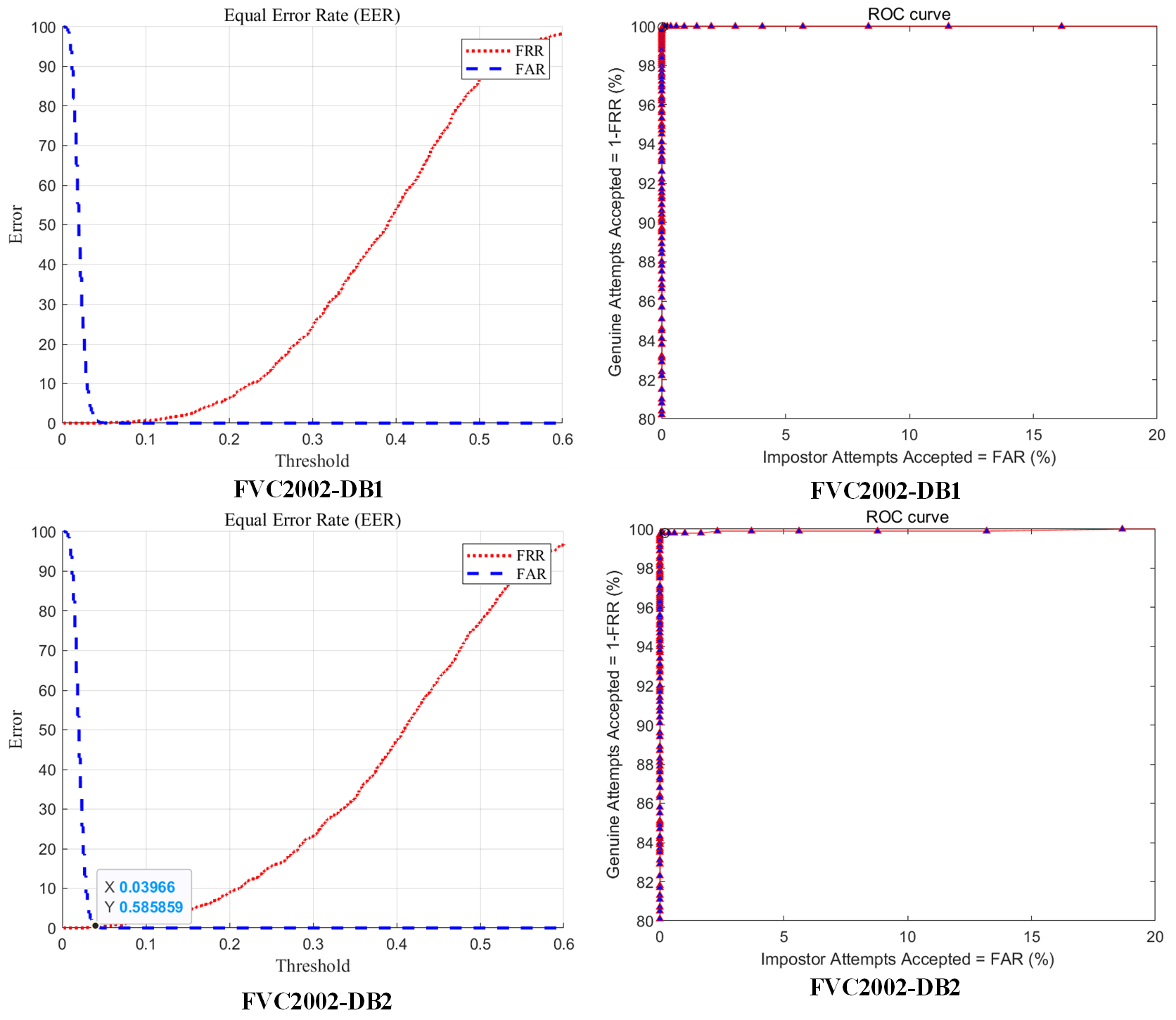
The experiment uses four public fingerprint datasets: FVC2002 DB1, DB2, and FVC2004 DB1, DB2, each containing 800 images from 100 users with 8 samples per finger. Following Jin’s method [28], get three samples are used for training and five for testing. The paper adopts the modified Polar Grid-based Three-Tuple Quantization (PGTQ) for feature extraction, which has an alignment-free property. Taking each minutia as a reference point, only neighboring minutiae within a 70-pixel radius are considered. After rotation-translation correction and polar coordinate conversion, they are quantized into triplets with steps of 10 pixels for radius, 20° for radial angle, and 30° for orientation angle. A polar grid containing more than one minutia is mapped to bit “1”, and finally, a variable-length binary vector is formed. Matching adopts a two-stage strategy consisting of local descriptor intersection matching and global score ratio calculation. Then evaluates system performance using genuine/imposter scores and the Equal Error Rate (EER), as per [29].
For each dataset, on an experimental platform with hardware configured as Intel(R) Core(TM) i5-12400F with 16 GB of memory, and software as MATLAB 9.12.0.1884302 (R2022a) , randomly generate 200 passwords of varying lengths as seeds, run 100 times, and record their minimum, maximum, average, and variance values. Figure 6 presents the EER and ROC results on FVC2002 DB1 and FVC2004 DB1. The ROC curves for DB1 (2002) and DB1 (2004) are nearly ideal, with steep curves approaching the top-left, indicating strong performance. As shown in Table 5, our method achieves the lowest EER on three datasets and performs competitively on the fourth. Compared to GRP hashing [10], our method significantly improves accuracy.
Table 5. EER Comparison between Proposed Method and Other Methods.
|
Methods |
FVC2002-DB1 |
FVC2002-DB2 |
FVC2004-DB1 |
FVC2004-DB2 |
|
|---|---|---|---|---|---|
|
GRP-based IoM hashing [10] |
0.22% |
0.47% |
4.74% |
3.99% |
|
|
URP-based IoM hashing [10] |
0.43% |
2.1% |
4.51% |
8.02% |
|
|
WSE hash [30] |
0.2% |
0.62% |
2.6% |
7.13% |
|
|
Bloom Filter [31] |
2.3% |
1.8% |
13.4% |
8.1% |
|
|
Ours |
Min |
0.00% |
0.07% |
2.91% |
3.60% |
|
Max |
0.30% |
0.55% |
4.09% |
4.84% |
|
|
Average |
0.14% |
0.29% |
3.37% |
4.39% |
|
|
Variance |
0.0036 |
0.0054 |
0.0442 |
0.0528 |
|
6.2. Unlinkability
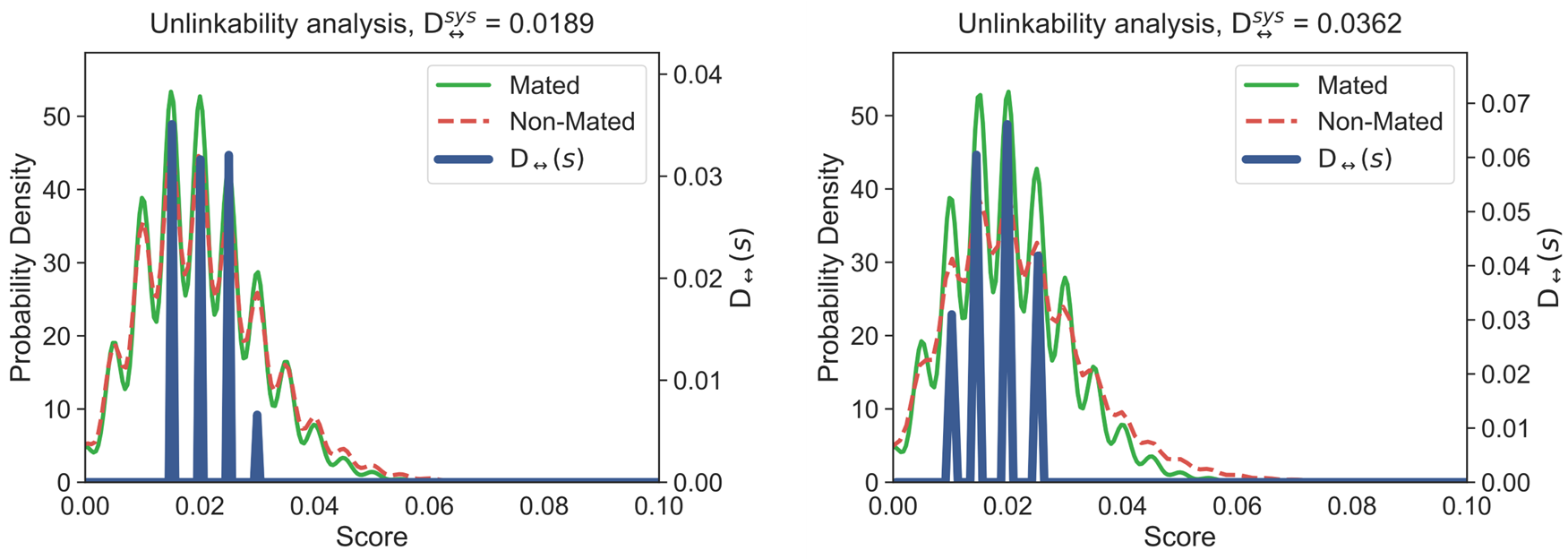
Biometric identification systems must satisfy unlinkability. This means that two or more repeatable templates generated from the same biometric features cannot be linked to each other, nor can it be inferred that they originate from the same biometric [4].
To verify that our proposed template protection scheme meets the requirement of unlinkability, we adopt a method proposed in [32] that uses a global metric $${D}_{↔}^{sys}$$ to evaluate the unlinkability of the system. $${D}_{↔}^{sys}$$ has values ranging from 0 to 1; $${D}_{↔}^{sys}$$ value of 1 suggests that the system is fully linkable, while a value of 0 indicates complete unlinkability. Generate 10 random keys as parameters to perform 10 transformations on each fingerprint vector, resulting in a total of 5000 transformed templates; and then calculate two scores for evaluation, namely Mated score and Non-Mated score. Based on these two evaluation scores, $${D}_{↔}^{sys}$$ is calculated. Figure 7 shows our assessment of the scheme using the FVC2002-DB1 and FVC2004-DB1 fingerprint databases.
6.3. Computation Cost
To intuitively analyze the performance of the proposed scheme, we compare its computational cost with that of existing protocols. Let $${T}_{h}$$, $${T}_{PUF}$$, $${T}_{FE}$$, and $${T}_{E/D}$$ denote the time required for hash operations, PUF evaluations, fuzzy extractor computation, and symmetric encryption/decryption (e.g., AES-128), respectively. Bitwise XOR operations are excluded due to negligible cost. Based on experimental results from [20] (The hardware configuration of this experiment is as follows: the user device adopts an HTC One smartphone, and the server uses an Intel Core i5-4300 machine; in terms of core technologies and tools, a 128-bit arbiter PUF is used for PUF operations, BCH code is adopted for the generation (FE.Gen) and reconstruction (FE.Rec) operations of the fuzzy extractor, and the JCE library is used to estimate the execution time of cryptographic operations) and [33] (The paper obtains the values of the operation times such as modular exponentiation and symmetric encryption/decryption through benchmark parameter setting and logical conversion. Instead of being derived from actual measurement through self-built hardware experiments, these values are based on standardized conversion supported by existing research conclusions in the field of cryptography), we adopt $${T}_{h}=0.056\, \mathrm{m}\mathrm{s}$$, $${T}_{PUF}=0.13\, \mathrm{m}\mathrm{s}$$, $${T}_{FE}=3\, \mathrm{m}\mathrm{s}$$, and $${T}_{E/D}=8.7\, \mathrm{m}\mathrm{s}$$. Accordingly, our mutual authentication phase completes in 74.408 ms: 21.164 ms for the user, 35.304 ms for the server, and 17.94 ms for the drone.
For comparison, other protocols incur costs from modular arithmetic and elliptic curve operations, with $${T}_{m}=16.84\,\mathrm{ }\mathrm{m}\mathrm{s}$$, $${T}_{eca}=4.4\mathrm{ }\,\mathrm{m}\mathrm{s}$$, and $${T}_{ecm}=17.1\, \mathrm{m}\mathrm{s}$$ [21]. As shown in Table 6, our scheme achieves lower computation overhead while maintaining strong security, unlike the overly lightweight design in [17], which compromises robustness.
Table 6. Computational Cost Comparisons.
|
Scheme |
User-Side Computation Cost |
Server-Side Computation Cost |
Drone-Side Computation Cost |
Total Cost |
|---|---|---|---|---|
|
[1] |
$$16{\mathrm{T}}_{\mathrm{h}}+{\mathrm{T}}_{\mathrm{F}\mathrm{E}}+5{\mathrm{T}}_{\mathrm{e}\mathrm{c}\mathrm{m}}+2{\mathrm{T}}_{\mathrm{e}\mathrm{c}\mathrm{a}}$$ |
$$10{\mathrm{T}}_{\mathrm{h}}+2{\mathrm{T}}_{\mathrm{e}\mathrm{c}\mathrm{m}}+{\mathrm{T}}_{\mathrm{e}\mathrm{c}\mathrm{a}}$$ |
$$7{\mathrm{T}}_{\mathrm{h}}+3{\mathrm{T}}_{\mathrm{e}\mathrm{c}\mathrm{m}}+{\mathrm{T}}_{\mathrm{e}\mathrm{c}\mathrm{a}}$$ |
193.448 ms |
|
[16] |
$$15{\mathrm{T}}_{\mathrm{h}}+2{\mathrm{T}}_{\mathrm{m}}$$ |
$$9{\mathrm{T}}_{\mathrm{h}}$$ |
$$7{\mathrm{T}}_{\mathrm{h}}$$ |
35.416 ms |
|
[17] |
$$8{\mathrm{T}}_{\mathrm{h}}+2{\mathrm{T}}_{\mathrm{E}/\mathrm{D}}+{\mathrm{T}}_{\mathrm{F}\mathrm{E}}$$ |
$$11{\mathrm{T}}_{\mathrm{h}}+6{\mathrm{T}}_{\mathrm{E}/\mathrm{D}}+{\mathrm{T}}_{\mathrm{F}\mathrm{E}}$$ |
$$6{\mathrm{T}}_{\mathrm{h}}+2{\mathrm{T}}_{\mathrm{E}/\mathrm{D}}+{\mathrm{T}}_{\mathrm{F}\mathrm{E}}+2{\mathrm{T}}_{\mathrm{P}\mathrm{U}\mathrm{F}}$$ |
97.66 ms |
|
[18] |
$$7{\mathrm{T}}_{\mathrm{h}}+3{\mathrm{T}}_{\mathrm{E}/\mathrm{D}}+{\mathrm{T}}_{\mathrm{e}\mathrm{x}\mathrm{p}}$$ |
$$2{\mathrm{T}}_{\mathrm{h}}+3{\mathrm{T}}_{\mathrm{E}/\mathrm{D}}+2{\mathrm{T}}_{\mathrm{e}\mathrm{x}\mathrm{p}}$$ |
3$${\mathrm{T}}_{\mathrm{h}}+2{\mathrm{T}}_{\mathrm{E}/\mathrm{D}}+{1\mathrm{T}}_{\mathrm{e}\mathrm{x}\mathrm{p}}$$ |
171.312 ms |
|
Ours |
$$9{\mathrm{T}}_{\mathrm{h}}+2{\mathrm{T}}_{\mathrm{P}\mathrm{U}\mathrm{F}}+2{\mathrm{T}}_{\mathrm{E}/\mathrm{D}}+{\mathrm{T}}_{\mathrm{E}\mathrm{F}}$$ |
$$9{\mathrm{T}}_{\mathrm{h}}+4{\mathrm{T}}_{\mathrm{E}/\mathrm{D}}$$ |
$$5{\mathrm{T}}_{\mathrm{h}}+2{\mathrm{T}}_{\mathrm{P}\mathrm{U}\mathrm{F}}+2{\mathrm{T}}_{\mathrm{E}/\mathrm{D}}$$ |
74.408 ms |
7. Conclusions
This paper proposes a method that combines the Fast Four Transform, Gaussian Random Projections, Position-Sensitive Hashing, Fuzzy Extractors, and Physical Unclonable Function to generate cancelable biometric templates, addressing the issue of permanent loss of biometric templates, and enhancing the protection of sensitive biometric data while ensuring strong resistance to known attacks. Experimental evaluations on FVC2002 and FVC2004 datasets demonstrate high accuracy and unlinkability. The complete AKA protocol introduced in this paper incorporates cancelable methods and PUF update schemes, allowing the generation of new templates by modifying parameters in case of data theft, ensuring security and efficiency. Formal security analysis using the ROR model and AVISPA simulation confirms the protocol’s robustness against replay, man-in-the-middle, and device-corruption attacks. Compared with existing protocols, our method achieves a better balance between security strength, computational efficiency, and biometric privacy, making it suitable for deployment in resource-constrained IoD environments.
Author Contributions
Conceptualization, K.C. and W.B.; Methodology, K.C.; Software, K.C.; Validation, K.C., W.B. and D.X.; Formal Analysis, K.C.; Investigation, Q.L.; Resources, W.B.; Data Curation, W.B.; Writing—Original Draft Preparation, K.C.; Writing—Review & Editing, W.B.; Visualization, J.M.; Supervision, W.B.; Project Administration, W.B.; Funding Acquisition, W.B. and D.X.
Ethics Statement
Not applicable.
Informed Consent Statement
Not applicable.
Data Availability Statement
Bundled with the book Handbook of Fingerprint Recognition (3rd Ed., Springer, 2022). Available via a formal license application to the FVC organizers (University of Bologna).
Funding
The work are partially supported by the National Natural Science Foundation of China (No. 61801004), Natural Science Foundation of Anhui Province (No. 2108085MF206).
Declaration of Competing Interest
The authors declare that they have no known competing financial interests or personal relationships that could have appeared to influence the work reported in this paper.
References
- Mekdad Y, Aris A, Babun L, Fergougui AE, Conti M, Lazzeretti R, et al. A survey on security and privacy issues of uavs. Comput. Netw. 2023, 224, 109626. DOI:10.1016/j.comnet.2023.109626 [Google Scholar]
- Gharibi M, Boutaba R, Waslander SL. Internet of drones. IEEE Access 2016, 4, 1148–1162. DOI:10.1109/ACCESS.2016.2537208 [Google Scholar]
- Li B, Fei Z, Zhang Y. Uav communications for 5g and beyond: Recent advances and future trends. IEEE Internet Things J. 2019, 6, 2241–2263. DOI:10.1109/JIOT.2018.2887086 [Google Scholar]
- Patel VM, Ratha NK, Chellappa R. Cancelable biometrics: A review. IEEE Signal Process. Mag. 2015, 32, 54–65. DOI:10.1109/MSP.2015.2434151 [Google Scholar]
- Choudhury B, Then P, Issac B, Raman V, Haldar MK. A survey on bio metrics and cancelable biometrics systems. Int. J. Image Graph. 2018, 18, 1850006. DOI:10.1142/S0219467818500067 [Google Scholar]
- Wang D, Cheng H, Wang P, Huang X, Jian G. Zipf’s law in passwords. IEEE Trans. Inf. Forensics Secur. 2017, 12, 2776–2791. DOI:10.1109/TIFS.2017.2721359 [Google Scholar]
- Manisha, Kumar N. Cancelable biometrics: A comprehensive survey. Artif. Intell. Rev. 2020, 53, 3403–3446. DOI:10.1007/s10462-019-09767-8 [Google Scholar]
- Teoh ABJ, Yuang CT. Cancelable biometrics realization with multispace ran dom projections. IEEE Trans. Syst. Man Cybern. Part B 2007, 37, 1096–1106. DOI:10.1109/TSMCB.2007.903538 [Google Scholar]
- Algarni AD, El Banby GM, Soliman NF, El-Samie FEA, Iliyasu AM. Efficient implementation of homomorphic and fuzzy transforms in random-projection encryption frameworks for cancellable face recognition. Electronics 2020, 9, 1046. DOI:10.3390/electronics9061046 [Google Scholar]
- Jin Z, Hwang JY, Lai YL, Kim S, Teoh ABJ. Ranking-based locality sen sitive hashing-enabled cancelable biometrics: Index-of-max hashing. IEEE Trans Actions Inf. Forensics Secur. 2018, 13, 393–407. DOI:10.1109/TIFS.2017.2753172 [Google Scholar]
- Kuzu RS, Piciucco E, Maiorana E, Campisi P. On-the-fly finger-vein-based biometric recognition using deep neural networks. IEEE Trans. Inf. Tion Forensics Secur. 2020, 15, 2641–2654. DOI:10.1109/TIFS.2020.2971144 [Google Scholar]
- Das ML. Two-factor user authentication in wireless sensor networks. IEEE Trans Actions Wirel. Commun. 2009, 8, 1086–1090. DOI:10.1109/TWC.2008.080128 [Google Scholar]
- Srinivas J, Das AK, Wazid M, Vasilakos AV. Designing secure user authentication protocol for big data collection in iot-based intelligent transportation system. IEEE Internet Things J. 2021, 8, 7727–7744. DOI:10.1109/JIOT.2020.3040938 [Google Scholar]
- Sarier ND. Practical multi-factor biometric remote authentication. In Proceedings of the 2010 Fourth IEEE International Conference on Biometrics: Theory, Applications and Systems (BTAS), Washington, DC, USA, 27–29 September 2010; pp. 1–6. [Google Scholar]
- Kirsal Ever Y. Secure-anonymous user authentication scheme for e-healthcare applica tion using wireless medical sensor networks. IEEE Syst. J. 2019, 13, 456–467. DOI:10.1109/JSYST.2018.2866067 [Google Scholar]
- Gope P, Das AK, Kumar N, Cheng Y. Lightweight and physically secureanonymous mutual authentication protocol for real-time data access in industrial wireless sensor networks. IEEE Trans. Ind. Inform. 2019, 15, 4957–4968. DOI:10.1109/TII.2019.2895030 [Google Scholar]
- Chaudhary D, Soni T, Vasudev KL, Saleem K. A modified lightweight au thenticated key agreement protocol for internet of drones. Internet Things 2023, 21, 100669. DOI:10.1016/j.iot.2022.100669 [Google Scholar]
- Liu Z, Guo C, Wang B. A physically secure, lightweight three-factor and anony mous user authentication protocol for iot. IEEE Access 2020, 8, 195914–195928. DOI:10.1109/ACCESS.2020.3034219 [Google Scholar]
- Tanveer M, Khan AU, Kumar N, Hassan MM. Ramp-iod: A robust authenticated key management protocol for the internet of drones. IEEE Internet Things J. 2022, 9, 1339–1353. DOI:10.1109/JIOT.2021.3084946 [Google Scholar]
- Bian W, Gope P, Cheng Y, Li Q. Bio-aka: An efficient fingerprint based two factor user authentication and key agreement scheme. Future Gener. Comput. Syst. 2020, 109, 45–55. DOI:10.1016/j.future.2020.03.034 [Google Scholar]
- Zhang H, Bian W, Jie B, Xu D, Zhao J. A complete user authentication and key agreement scheme using cancelable biometrics and puf in multi-server environment. IEEE Trans. Inf. Forensics Secur. 2021, 16, 5413–5428. DOI:10.1109/TIFS.2021.3128826 [Google Scholar]
- Hu Y, Bian W, Xie D, Xu D, Xu Z. Secure and efficient industrial wireless sensor networks protocol based on cancelable biometrics. IEEE Trans. Ind. Inform. 2024, 20, 13580–13590. DOI:10.1109/TII.2024.3423309 [Google Scholar]
- Dolev D, Yao A. On the security of public key protocols. IEEE Trans. Inf. Theory 1983, 29, 198–208. DOI:10.1109/TIT.1983.1056650 [Google Scholar]
- Zhang J, Qu G. Physical unclonable function-based key sharing via machine learning for iot security. IEEE Trans. Ind. Electron. 2020, 67, 7025–7033. DOI:10.1109/TIE.2019.2938462 [Google Scholar]
- Ghammam L, Karabina K, Lacharme P, Thiry-Atighehchi K. A cryptanal ysis of two cancelable biometric schemes based on index-of-max hashing. IEEE Trans. Inf. Forensics Secur. 2020, 15, 2869–2880. DOI:10.1109/TIFS.2020.2977533 [Google Scholar]
- Li Y, Pang L, Zhao H, Cao Z, Liu E, Tian J. Indexing-min–max hashing: Relaxing the security–performance tradeoff for cancelable fingerprint templates. IEEE Trans. Syst. Man Cybern. Syst. 2022, 52, 6314–6325. DOI:10.1109/TSMC.2022.3144854 [Google Scholar]
- Vigano L. Automated Security Protocol Analysis With the AVISPA Tool. Electron. Notes Theor. Comput. Sci. 2006, 155, 61–86. DOI:10.1016/j.entcs.2005.11.052 [Google Scholar]
- Jin Z, Lim MH, Teoh ABJ, Goi BM, Tay YH. Generating fixed-length representation from minutiae using kernel methods for fingerprint authentication. IEEE Trans. Syst. Man Cybern. Syst. 2016, 46, 1415–1428. DOI:10.1109/TSMC.2015.2499725 [Google Scholar]
- Cappelli R, Maio D, Maltoni D, Wayman JL, Jain AK. Performance eval uation of fingerprint verification systems. IEEE Trans. Pattern Anal. Mach. Intell. 2006, 28, 3–18. DOI:10.1109/TPAMI.2006.20 [Google Scholar]
- Kong XJ, Li XJ, Jin Z, Zhou P, Chen JY. One-factor cancellable bio metrics verification scheme. Acta Autom. Sin. 2021, 47, 1159–1170. DOI: 10.16383/j.aas.c190059. [Google Scholar]
- Li G, Yang B, Rathgeb C, Busch C. Towards generating pro tected fingerprint templates based on bloom filters. In Proceedings of the 3rd International Workshop on Biometrics and Forensics (IWBF 2015), Gjovik, Norway, 3–4 March 2015; pp. 1–6. [Google Scholar]
- Gomez-Barrero M, Galbally J, Rathgeb C, Busch C. General framework to evaluate unlinkability in biometric template protection systems. IEEE Trans. Inf. Forensics Secur. 2018, 13, 1406–1420. DOI:10.1109/TIFS.2017.2788000 [Google Scholar]
- Li CT, Hwang MS, Chu YP. A secure and efficient communication schemewith authenticated key establishment and privacy preserving for vehicular ad hoc networks. Comput. Commun. 2008, 31, 2803–2814. DOI:10.1016/j.comcom.2007.12.005 [Google Scholar]